IPhone: Google uncovers an iOS kit used for crypto phishing
A sophisticated exploitation kit targeting iPhones has been revealed by Google. Named Coruna, it is used to steal cryptos via phishing attacks. An analysis of a major threat for iOS users in 2026.

In brief
- Google reveals an iOS kit named Coruna used to steal cryptos via phishing attacks, targeting iPhones (versions 13.0 to 17.2.1).
- The Coruna kit exploits iOS vulnerabilities to extract crypto wallet recovery phrases via malicious websites.
- To protect against Coruna, it is crucial to update your iPhone, enable lockdown mode, and avoid suspicious crypto-related links.
Google reveals Coruna, a crypto phishing kit targeting iOS users
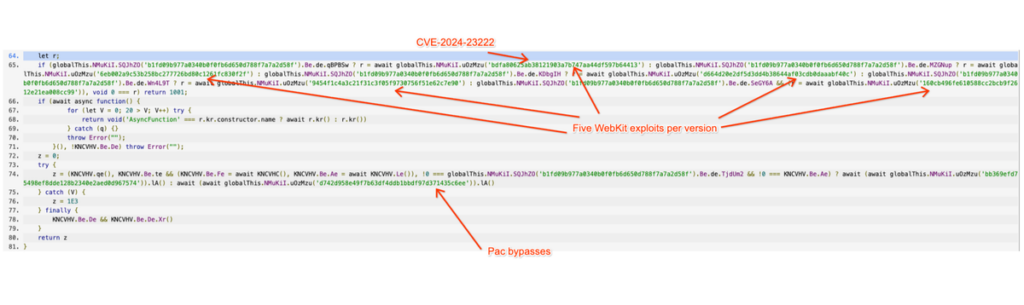
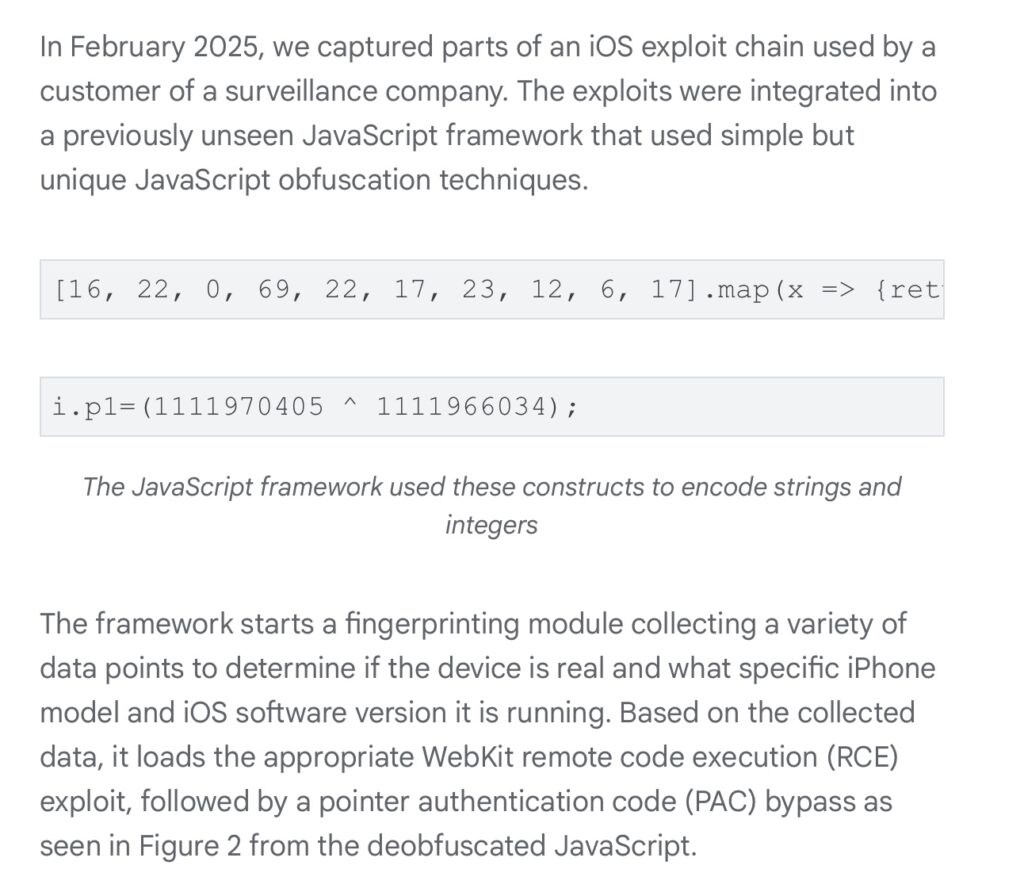
In February 2025, the Google Threat Intelligence Group (GTIG) discovered Coruna, an exploitation kit specifically targeting Apple devices running iOS (versions 13.0 to 17.2.1). Indeed, this kit uses advanced exploit chains to compromise iPhones via malicious websites! Often, fake crypto sites.
Once the device is infected, Coruna extracts the crypto wallet recovery phrases, passwords, and other sensitive data. GTIG revealed that Coruna has been used by malicious actors to target iPhone users through phishing campaigns. These attacks generally occur in multiple stages:
- The user is prompted to visit a compromised site, where a JavaScript script identifies the device and delivers the appropriate exploit;
- Victims, often cryptocurrency holders, have their assets stolen in seconds.
The origin of Coruna remains unclear, but GTIG noted similarities with tools previously attributed to state groups. The kit was spotted on fake Chinese crypto sites, as well as in attacks targeting Ukrainian users. Google alerted Apple, which has since fixed some vulnerabilities. However, the threat persists for devices not updated.
Crypto phishing: how to protect yourself from Coruna?
To avoid becoming a victim of Coruna, the first step is to update your iPhone to the latest iOS version. Apple has released patches for the vulnerabilities exploited by this kit. This makes updated devices immune to this threat. Next, also enable Lockdown Mode, a feature designed to block sophisticated attacks like Coruna.
Additionally, avoid clicking on suspicious links, especially from sites or emails related to crypto. Always verify the authenticity of URLs and prioritize official platforms for your transactions. Finally, use hardware wallets to store your cryptocurrencies (bitcoin, ethereum…). These offer an extra layer of security against online attacks.
The revelation of Coruna by Google reminds us that crypto phishing attacks are becoming increasingly sophisticated. Although solutions exist, protecting your assets primarily depends on your vigilance. The question remains: are users ready to adopt best practices to guard against these constantly evolving threats?
Maximize your Cointribune experience with our "Read to Earn" program! For every article you read, earn points and access exclusive rewards. Sign up now and start earning benefits.
The world is evolving and adaptation is the best weapon to survive in this undulating universe. Originally a crypto community manager, I am interested in anything that is directly or indirectly related to blockchain and its derivatives. To share my experience and promote a field that I am passionate about, nothing is better than writing informative and relaxed articles.
The views, thoughts, and opinions expressed in this article belong solely to the author, and should not be taken as investment advice. Do your own research before taking any investment decisions.